In today’s digital world, our personal and professional data constantly travels across the Internet or is stored on servers. Information like passwords, credit card numbers, or medical records is highly sensitive. To protect it, one of the most important methods is encryption. But what exactly is encryption, and how does it work?
1. What is Encryption?
Encryption is a process that transforms readable information (plaintext) into an unreadable format (ciphertext) using an algorithm and a key.
– Plaintext: “My password is 1234”
– Ciphertext: “U2FsdGVkX19JH23…” (unintelligible without the key)
The main goal is simple: if someone intercepts the encrypted data, they cannot read it without the decryption key.
2. Why Encrypt Data?
Encryption allows you to:
– Ensure confidentiality – only authorized people can access the information.
– Protect against theft and hacking – even if data is stolen, it remains useless without the key.
– Guarantee data integrity – some encryption methods detect if data has been altered.
– Comply with regulations – for example, GDPR in Europe requires personal data to be secured.
3. Main Types of Encryption
There are two main categories of encryption:
Symmetric Encryption
– Principle: The same key is used to encrypt and decrypt data.
– Common algorithms: AES (Advanced Encryption Standard), DES (Data Encryption Standard).
– Advantages: Fast and efficient for large amounts of data.
– Disadvantages: The key must be shared between sender and receiver. If intercepted, security is compromised.
Example:
Alice wants to send a message to Bob. She encrypts it with a secret key, and Bob uses the same key to decrypt it.
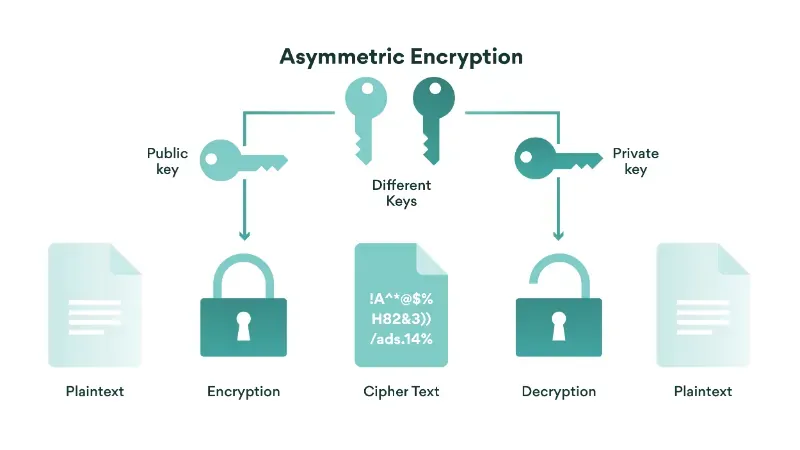
Asymmetric Encryption
– Principle: Two keys are used:
– Common algorithms: RSA, ECC (Elliptic Curve Cryptography).
– Advantages: No need to share the private key, which increases security.
– Disadvantages: Slower than symmetric encryption, so usually used for small data or key exchange.
Example:
Bob shares his public key with Alice. She encrypts her message with it, and only Bob can decrypt it using his private key.
4. Encryption in Everyday Life
Encryption is everywhere around us:
– HTTPS websites – protect your bank information and passwords.
– Secure messaging apps – WhatsApp, Signal, or Telegram encrypt conversations.
– Cloud storage – files are encrypted to remain private.
– Operating systems – Windows BitLocker or macOS FileVault encrypt the hard drive to protect files.
5. Best Practices for Encryption
– Use long, complex keys – the longer the key, the harder it is to crack.
– Update algorithms regularly – old algorithms like DES are now vulnerable.
– Protect private keys – never share or store them insecurely.
– Combine symmetric and asymmetric encryption – as used in HTTPS, combining speed and security.
6. Limitations of Encryption
Even though encryption is powerful, it is not infallible:
– If the key is stolen or poorly protected, encryption is useless.
– Humans are often the weakest link: weak passwords, phishing attacks, etc.
– Future quantum computers may break some current algorithms, although post-quantum cryptography is being developed.
Conclusion
Encryption is essential for data security. It ensures that your information remains confidential, even in case of theft or interception. Understanding the different types of encryption and following best practices helps protect your data and others’ information.
(websiteplanet.com)
(nordpass.com)
(cyberpress.org)
(euroweeklynews.com)
(proton.me)
(reddit.com)
(chatgpt.com)