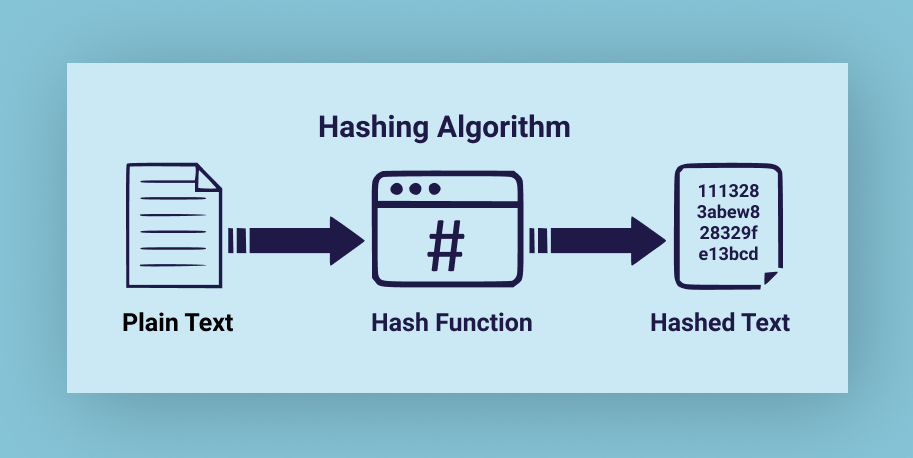
Result of a mathematical calculation applied to a password in order to avoid storing it in plain text.
Advantages:
- Data is never stored in plain text.
- Non-reversible.
Very useful when it comes to storing passwords.
Disadvantages:
- Two different inputs can produce the same hash.
Due to the way hashing works (mathematical computation), it is possible for two different inputs to generate the same hash value. - Irreversibility.
When storing data, irreversibility becomes a disadvantage if the original data needs to be retrieved.
Situations where it is useful:
- Password security: Systems do not store passwords in plain text, but rather their “hash” (fingerprint) to protect users in the event of a database breach.
- File integrity verification: Checking that a downloaded file has not been corrupted or modified by comparing its signature (MD5, SHA-256) with the original one.
- Blockchain and cryptocurrencies: Ensuring the immutability and security of transactions by linking each block to the previous one through a unique fingerprint.
Situations where it is not necessary:
- Small volumes of data: For a small number of elements, the computational and memory overhead related to hashing (collision management, hash functions) makes a simple table or encryption more efficient.
- Storage of data that must be retrieved: Hashing is a one-way function. If you need to recover the original value, you should not use hashing.
Pingback: ciproflox
Pingback: diflucan over the counter uk